Tuesday’s election resulted in a prisoner, dead pimp, and man with a thing for Bigfoot erotica all winning offices. We truly do live in the best timeline.
Tag: You’re Doing it Right
Deafening the Bug
I know a lot of people who put a piece of tape over their computer’s webcam. While this is a sane countermeasure, I’m honestly less worried about my webcam than the microphone built into my laptop. Most laptops, unfortunately, lack a hardware disconnect for the microphone and placing a piece of tap over the microphone input often isn’t enough to prevent it from picking up sound in whatever room it’s located. Fortunately, Apple has been stepping up its security game and now offers a solution to the microphone problem:
Little was known about the chip until today. According to its newest published security guide, the chip comes with a hardware microphone disconnect feature that physically cuts the device’s microphone from the rest of the hardware whenever the lid is closed.
“This disconnect is implemented in hardware alone, and therefore prevents any software, even with root or kernel privileges in macOS, and even the software on the T2 chip, from engaging the microphone when the lid is closed,” said the support guide.
The camera isn’t disconnected, however, because its “field of view is completely obstructed with the lid closed.”
While I have misgivings with Apple’s recent design and business decisions, I still give the company credit for pushing hardware security forward.
Implementing a hardware cutoff for the microphone doesn’t require something like Apple’s T2 chip. Any vendor could put a hardware disconnect switch on their computer that would accomplish the same thing. Almost none of them do though, even if they include hardware cutoffs for other peripherals (my ThinkPad, for example, has a build in cover for the webcam, which is quite nice). I hope Apple’s example encourages more vendors to implement some kind of microphone cutoff switch because being able to listen to conversations generally allows gathering more incriminating evidence that merely being able to look at whatever is in front of a laptop.
Good News from the Arms Race
Security is a constant arms race. When people celebrate good security news, I caution them from getting too excited because bad news is almost certainly soon to follow. Likewise, when people are demoralized by bad security news, I tell them not to lose hope because good news is almost certainly soon to follow.
Earlier this year news about a new smartphone cracking device called GrayKey broke. The device was advertised as being able to bypass the full-disk encryption utilized by iOS. But now it appears that iOS 12 renders GrayKey mostly useless again:
Now, though, Apple has put up what may be an insurmountable wall. Multiple sources familiar with the GrayKey tech tell Forbes the device can no longer break the passcodes of any iPhone running iOS 12 or above. On those devices, GrayKey can only do what’s called a “partial extraction,” sources from the forensic community said. That means police using the tool can only draw out unencrypted files and some metadata, such as file sizes and folder structures.
Within a few months I expect the manufacturer of the GrayKey device to announce an update that gets around iOS’s new protections and within a few months of that announcement I expect Apple to announce an update to iOS that renders GrayKey mostly useless again. But for the time being it appears that law enforcers’ resources for acquiring data from a properly secured iOS device are limited.
Reduced Competition
Pat Robertson appealed to the people of the United States to overlook the Saudis’ minor transgression of butchering a journalist because a $100 billion weapons sale was on the table. Not only does it appear as though those weapons sales will continue but there may actually be more! One of the United States’ competitors has announced its intention of pulling out of future arms deal with Saudi Arabia:
BERLIN — In a move that could put further pressure on President Trump to stop arms sales to Saudi Arabia, German Chancellor Angela Merkel announced Sunday evening that her government would not approve new arms exports to the kingdom until further notice.
If the United States can exploit Germany’s decision, it could ensure that Germany never gets another arms deal with Saudi Arabia. That would put the United States one step closer to being the despotic regime’s sole arms dealer! U-S-A! U-S-A! U-S-A!
The End of TLS 1.0 and 1.1
Every major browser developer has announced that they will drop support for Transport Layer Security (TLS) 1.0 and 1.1 by 2020:
Apple, Google, Microsoft, and Mozilla have announced a unified plan to deprecate the use of TLS 1.0 and 1.1 early in 2020.
TLS (Transport Layer Security) is used to secure connections on the Web. TLS is essential to the Web, providing the ability to form connections that are confidential, authenticated, and tamper-proof. This has made it a big focus of security research, and over the years, a number of bugs that had significant security implications have been found in the protocol. Revisions have been published to address these flaws.
Waiting until 2020 gives website administrators plenty of time to upgrade their sites, which is why I’ll be rolling my eyes when the cutoff date arrives and a bunch of administrators whine about the major browsers “breaking” their websites.
Every time browser developers announced years ahead of time that support will be dropped for some archaic standard, there always seems to be a slew of websites, include many major websites, that continue relying on the dropped standard after the cutoff date.
The First Candidate with a Convincing Argument
John McAfee is the first presidential candidate for this election cycle with a valid argument for electing him:
.@VerminSupreme and myself at the 2016 Libertarian National Convention. If that one chance in a trillion that I could be elected president actually happens, I will stand down and be replaced by him. Vermin would be the best president ever.
This looks like a winning team to me:
The Power of Not Voting
People like to talk about the power of voting but few bother to mention the power of not voting:
BUCHAREST (Reuters) – A referendum to change Romania’s constitution to prevent same sex couples from securing the right to marry failed to draw enough voters to validate the result on Sunday, after a campaign that led to a rise in hate speech against the gay community.
[…]
Dozens of human rights groups had said a successful referendum would embolden further attempts to chip away at the rights of minority groups and push Romania onto a populist, authoritarian track.
They have encouraged people to boycott the ballot, with several companies and popular musicians and artists following. A library chain even offered a book discount over the weekend for those who wanted to stay in and read rather than vote.
If voter turnout had been higher, the referendum may have passed. Since not enough people bothered to show up to validate the results, the referendum couldn’t pass.
Governments that describe themselves as democratic prefer to make it appear as though their power is endorse by “the people.” That means that they like to see high voter turnout. If a vast majority of people go to the polls during an election, a government can argue that it enjoys the endorsement of the majority of “the people.” If almost nobody shows up during an election, a government has a much tougher time making that claim.
Properly Warning Users About Business Model Changes
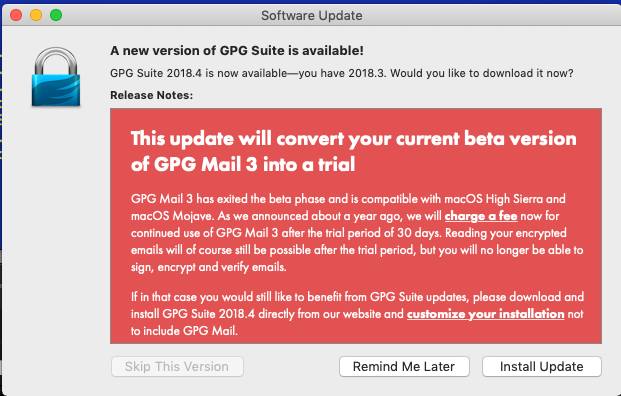
I have an update from my previous article about how the developers of GPGTools botched their changeover from offering a free software suite to a paid software suite. It appears that they listened to those of us who criticized them for not properly notifying their users that the latest update will change the business model because this is the new update notification:
That’s how you properly inform your users about business model changes.
Cloudflare Makes Tor Use More Bearable
One of the biggest annoyances of using the Tor Browser is that so many sites that rely on Cloudflare services throw up CAPTCHA challenges before allowing you to view content. Yesterday Cloudflare announced a change to its service that should make life more bearable for Tor users:
Cloudflare launched today a new service named the “Cloudflare Onion Service” that can distinguish between bots and legitimate Tor traffic. The main advantage of this new service is that Tor users will see far less, or even no CAPTCHAs when accessing a Cloudflare-protected website via the Tor Browser.
The new Cloudflare Onion Service needed the Tor team to make “a small tweak in the Tor binary,” hence it will only work with recent versions of the Tor Browser –the Tor Browser 8.0 and the new Tor Browser for Android, both launched earlier this month.
Hallelujah!
The Power of Public Shaming
Every major security breach is followed by calls for politicians to enact more stringent regulations. When I see people demanding additional government regulations I like to point out that there is a list of alternative solutions that can yield far better results (especially since regulations, being a product of government, are extremely rigid and slow to change, which makes them a solution ill-suited to fast moving markets). One of those solutions is public shaming. It turns out that public shaming is often a viable solution to security issues:
See the theme? Crazy statements made by representatives of the companies involved. The last one from Betfair is a great example and the entire thread is worth a read. What it boiled down to was the account arguing with a journalist (pro tip: avoid arguing being a dick to those in a position to write publicly about you!) that no, you didn’t just need a username and birth date to reset the account password. Eventually, it got to the point where Betfair advised that providing this information to someone else would be a breach of their terms. Now, keeping in mind that the username is your email address and that many among us like cake and presents and other birthday celebratory patterns, it’s reasonable to say that this was a ludicrous statement. Further, I propose that this is a perfect case where shaming is not only due, but necessary. So I wrote a blog post..
Shortly after that blog post, three things happened and the first was that it got press. The Register wrote about it. Venture Beat wrote about it. Many other discussions were held in the public forum with all concluding the same thing: this process sucked. Secondly, it got fixed. No longer was a mere email address and birthday sufficient to reset the account, you actually had to demonstrate that you controlled the email address! And finally, something else happened that convinced me of the value of shaming in this fashion:
A couple of months later, I delivered the opening keynote at OWASP’s AppSec conference in Amsterdam. After the talk, a bunch of people came up to say g’day and many other nice things. And then, after the crowd died down, a bloke came up and handed me his card – “Betfair Security”. Ah shit. But the hesitation quickly passed as he proceeded to thank me for the coverage. You see, they knew this process sucked – any reasonable person with half an idea about security did – but the internal security team alone telling management this was not cool wasn’t enough to drive change.
As I mentioned above, regulations tend to be rigid and slow to change. Public shaming on the other hand is often almost instantaneous. It seldom takes long for a company tweet that makes an outrageous security claim to be bombarded with criticism. Within minutes there are retweets by people mocking the statement, replies from people explaining why the claim is outrageous, and journalists writing about how outrageous the claim is. That public outrage, unlike C-SPAN, quickly reaches the public at large. Once the public becomes aware of the company’s claim and why it’s bad, the company has to being worrying about losing customers and by extent profits.